Business success hinges on more than just talent, it’s built on trust and verified credentials. With evolving compliance laws, insider threats, and a remote workforce, knowing exactly who we hire has never mattered more. KYE (Know Your Employee) empowers organizations to verify employee identities, mitigate fraud, and safeguard sensitive operations from day one. In this comprehensive guide, we’ll demystify KYE, explain how it goes beyond KYC and KYB, and walk through the steps, technologies, and regulatory demands shaping employee onboarding and ongoing verification in 2026. Let’s explore how robust KYE frameworks not only help us stay compliant, but also create a safer, more productive workplace.
Key Takeaways
- KYE (Know Your Employee) is essential for verifying employee identities and credentials, strengthening trust and compliance within organizations.
- Unlike KYC and KYB, KYE focuses inwardly on verifying employees to prevent insider threats, fraud, and ensure authorized access.
- A robust KYE framework includes identity verification, background checks, continuous monitoring, access control, and employee training for ongoing security.
- Integrating biometric and document verification during onboarding enhances security by detecting fraud and confirming authentic identities.
- Automating KYE processes with AI and digital tools improves efficiency, accuracy, and regulatory compliance while reducing HR burden.
- Continuous KYE throughout the employee lifecycle enables risk detection, access reevaluation, and maintains a culture of integrity and vigilance.
Understanding the Importance of KYE and Employee Verification
A workplace is only as secure as its people. That’s why employee verification, at the core of KYE, has become an essential business requirement. KYE involves a thorough process to verify that employees are who they say they are, confirming credentials, work history, and legal status. This isn’t just about compliance: it’s about building a culture of trust and integrity.
Unfortunately, organizations that skip comprehensive KYE open themselves to serious risks. Unverified personnel can result in internal fraud, accidental breaches, or deliberate sabotage. Even a single unchecked employee can compromise data protection, drain resources, or erode trust among clients and colleagues. On the other hand, robust KYE significantly reduces the risk of hiring fraudulent or unqualified candidates and ensures access is reserved for authorized personnel only.
Employee verification is also vital for complying with regulations like AML (Anti-Money Laundering) and counter-terrorism rules. Performing KYE checks enables us to identify potential risks early, prevent fraudulent activity, and maintain a work environment where every team member is qualified and vetted.
How KYE Differs From KYC and KYB Processes
KYE, KYC (Know Your Customer), and KYB (Know Your Business) revolve around identity verification, but their focus and execution differ sharply. KYC is primarily used by financial institutions to verify the identity of clients, helping prevent money laundering and fraud. KYB extends this verification to companies interacting with each other, ensuring the legitimacy of business partners and suppliers.
KYE, meanwhile, focuses on verifying employees, the people inside our organization who have access to sensitive systems, data, and resources. While KYC and KYB look outward, KYE looks inward. Employee background checks, credential verification, and continuous monitoring are all part of a robust KYE strategy, ensuring internal trust and compliance. This focus on internal stakeholders means KYE helps prevent insider threats and addresses internal fraud before it escalates.
In many industries, especially those regulated under AML or data protection laws, KYE is now a legal requirement, a reflection of its distinct importance from traditional customer or business checks.
Core Elements of a Robust KYE Framework
Building an effective KYE program isn’t just ticking a box, it’s about designing a system that covers every angle of employee verification and ongoing risk management. Comprehensive KYE frameworks typically include:
- Identity Verification: Confirming that employees are who they claim to be, often via government-issued ID, biometrics, and digital verification platforms.
- Credential and Background Checks: Assessing education, licensing, and employment history to validate work experience and legal compliance.
- Ongoing Monitoring: Automating alerts for changes in employee status, new criminal activity, or other emerging risks.
- Access Control and Privileges Management: Ensuring the right people have access to the right systems, no more, no less.
- Policy and Training: Educating staff about KYE protocols and the broader importance of workplace integrity.
By weaving these elements into our hiring and HR processes, we can proactively address vulnerabilities, reduce the risk of internal fraud, and safeguard organizational assets. A thorough KYE ensures every team member is both trustworthy and properly qualified throughout their tenure.
The KYE Process: Verifying Employee Identities and Backgrounds
Successful KYE relies on a multi-step, thorough approach to verifying employee identities and backgrounds, never just a cursory ID check. Here’s what an effective know your employee process typically includes:
- Collection of Personal Information: We begin by gathering essential employee data: name, date of birth, government ID, contact details, and any relevant credential documentation.
- Identity and Document Verification: Using reliable platforms, we verify the authenticity of official documentation, ensuring there are no forgeries or mismatches.
- Background Screening: Comprehensive checks include education verification, employment history, and sometimes even criminal record and credit checks, always in line with local laws.
- Credential Validation: Especially for regulated roles, it’s crucial to confirm professional licenses or certifications.
- Continuous Compliance Monitoring: We don’t set and forget: employee statuses are rechecked periodically or when roles or responsibilities change.
Every step in this process is crucial for identifying potential risks and minimizing the likelihood of hiring or retaining individuals who could endanger company assets or reputation. By implementing an effective KYE process, we maintain a secure, productive, and compliant work environment.
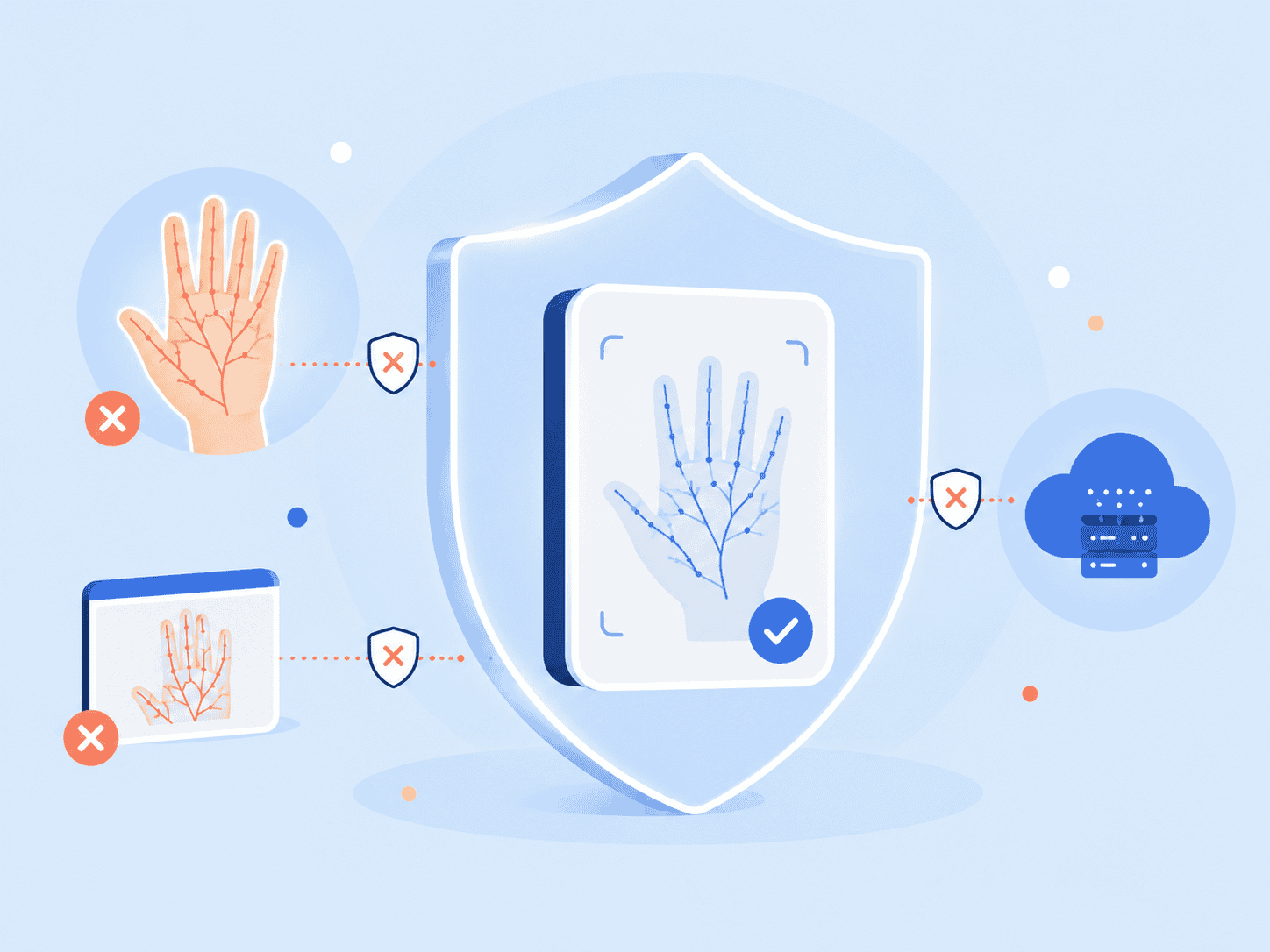
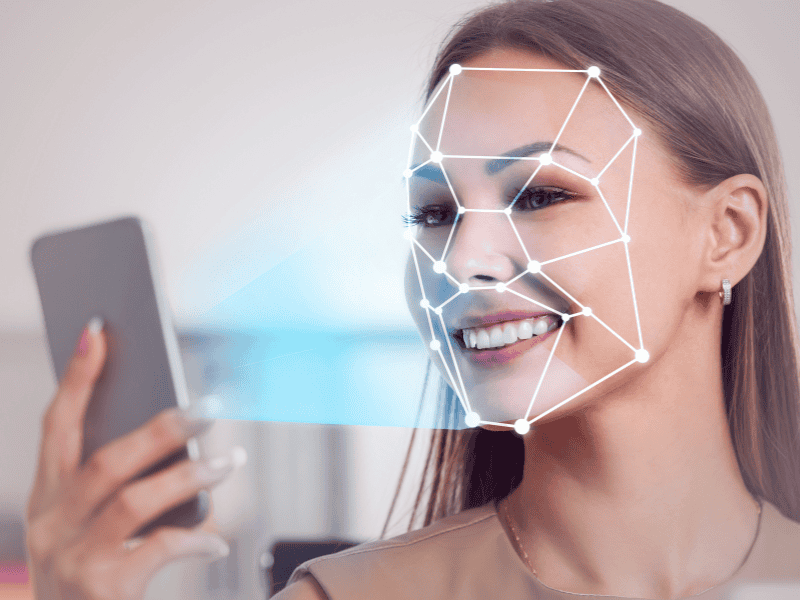
Biometric and Document Verification: Enhancing Security During Employee Onboarding
Traditional checks alone don’t always suffice in verifying an employee’s identity. Fraudsters have grown more sophisticated, skillful enough to forge documents or falsify identities. That’s where biometric verification comes into play during employee onboarding.
Biometrics, such as facial recognition, fingerprint scans, or voice authentication, can confirm that the person presenting credentials is the true owner. Combined with document verification, this two-pronged approach effectively blocks many forms of social engineering and identity fraud. When we ask new hires to provide physical or digital ID documents, advanced systems validate features like watermarks, MRZ codes, and embedded security chips alongside biometric data.
These next-generation security protocols help us:
- Detect forged or stolen credentials instantly.
- Prevent fraudulent access to sensitive systems right from the start.
- Strengthen our ability to meet evolving regulatory compliance needs.
By integrating biometric and document verification into our onboarding process, we create a strong first defense and reinforce a culture of security from the outset.
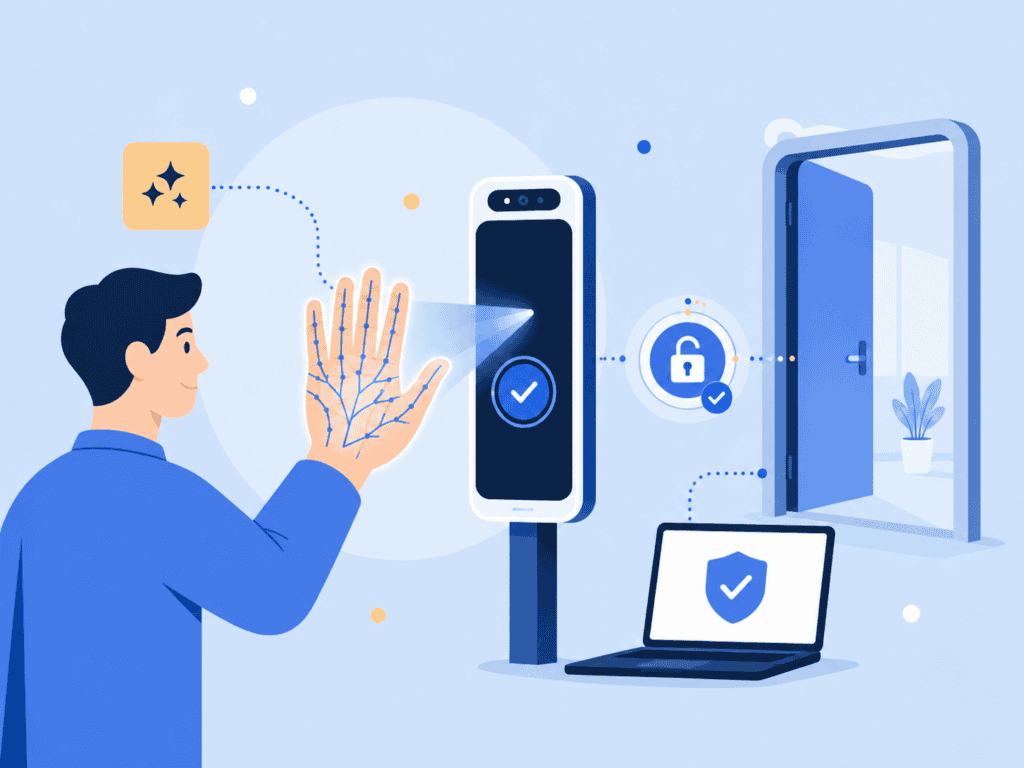
Integrating KYE into Employee Onboarding and Access Control
Deploying KYE during onboarding and aligning it with access control systems streamlines our risk management and compliance efforts. Effective integration works in several ways:
- Seamless Experience for New Employees: Automated KYE checks can reduce the time-to-hire without sacrificing security, boosting employee satisfaction and productivity from day one.
- Conditional Access Privileges: Based on verification results, we assign appropriate access levels, ensuring that only fully verified staff enter sensitive areas or systems.
- Centralized Data Management: Securely storing employee KYE data allows HR and security teams to quickly update access as roles evolve or offboarding becomes necessary.
A robust KYE-integrated onboarding process guarantees we’re not just vetting new hires but also strengthening our ability to control who accesses what, when, and why. Without KYE integration, there’s always a risk of unintended insider access or compliance gaps, both of which threaten business continuity.
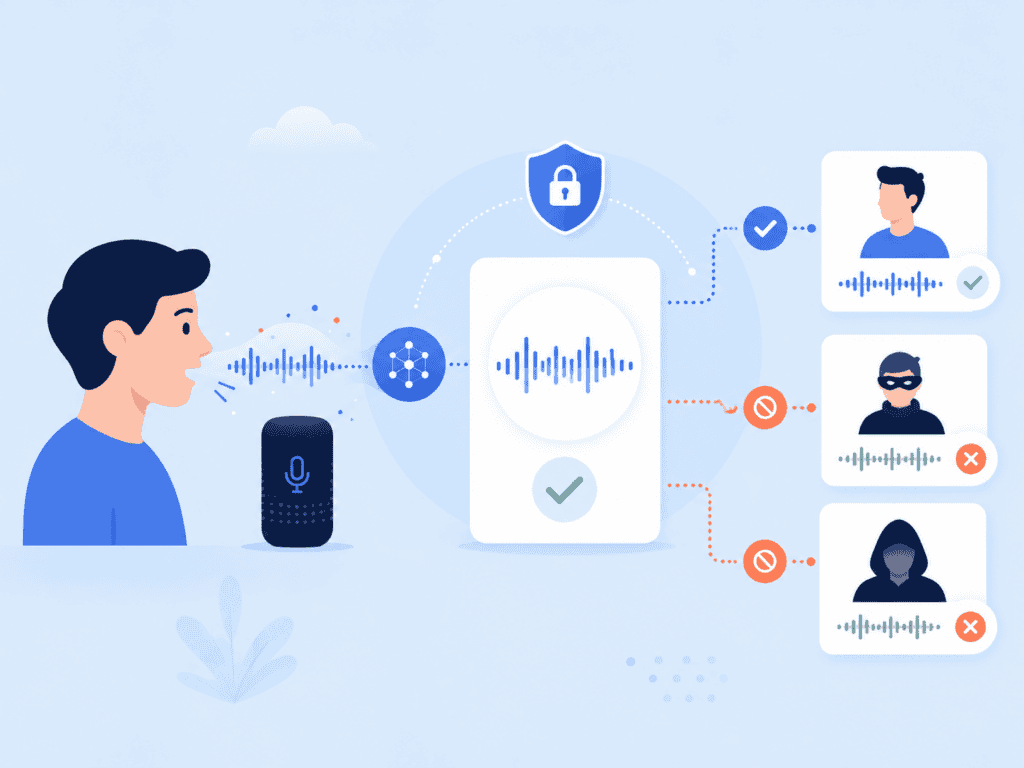
Internal Fraud and Insider Threats: Mitigating Risks With KYE
No organization is immune to insider threats. The risk of employee fraud, from data theft to financial misappropriation, increases when verification protocols are lacking. KYE stands as a frontline defense against these threats by ensuring robust, ongoing verification of current staff and potential hires alike.
Fraudulent behavior can come from any tier within an organization. Even highly trusted individuals have, on occasion, exploited weak identity verification or access controls. By rigorously validating every employee’s background, credentials, and access privileges, we drastically lower the likelihood of such incidents.
Also, real-time KYE monitoring tools now send alerts about suspicious activity, status changes, or deviations from established work patterns. When these systems work in tandem with internal controls, it’s far easier to detect, investigate, and address anomalies before they escalate into costly breaches or legal trouble. KYE provides peace of mind, knowing that risk and fraud are proactively managed across every department.
KYE for Regulatory and AML Compliance: Navigating Legal Requirements
Regulatory compliance is a moving target, especially as employee-centric laws become ever more complex. In sectors like finance and healthcare, KYE isn’t just smart practice, it’s often mandatory. Regulators demand that organizations verify the identities and backgrounds of their workforces to guard against fraud, money laundering, and other criminal behaviors.
Anti-Money Laundering (AML) frameworks, in particular, require ongoing KYE monitoring to detect and report suspicious activities. Non-compliance can result in hefty fines, legal penalties, or reputational harm. That’s why comprehensive KYE procedures include:
- Documented employee screening processes
- Secure storage of verification records
- Transparent reporting and audit trails
We must also stay vigilant with changes in regional and international compliance standards. KYE helps ensure not only that our practices are legal, but that we can demonstrate proactive risk mitigation in the face of audits or investigations. By making KYE central to our regulatory strategy, we avoid pitfalls and protect our organization’s future.
Automating and Streamlining KYE: Leveraging Technology for Efficiency
Manual KYE checks are time-consuming and error-prone, placing undue burden on HR and compliance teams. Today’s digital solutions can automate much of the process, boosting both efficiency and security. Platforms leveraging artificial intelligence, optical character recognition, and deep learning can verify identities, assess credentials, and perform background checks nearly instantaneously.
Other technologies that streamline KYE include:
- Digital Onboarding Portals: Integrate verification, credential checks, and compliance documentation in a single flow.
- Automated Alert Systems: Notify us of changes to an employee’s risk status, expediting necessary reviews.
- Seamless HR Integrations: Enable ongoing KYE monitoring and easier regulatory reporting.
Not only does this automation reduce human error and save valuable hours, but it ensures every hire meets our risk management and compliance needs. The key is balancing automation with oversight, ensuring that no alerts or critical details are missed in the drive for speed.
Continuous KYE: Strengthening Your Risk Management Throughout the Employee Lifecycle
KYE isn’t a one-and-done affair. Risks shift and employees’ roles evolve over time, so a continuous KYE approach protects us from new threats throughout every staff member’s tenure. Routine reverification of credentials, updated background checks, and real-time monitoring are pillars of an ongoing KYE program.
With continuous KYE, we can:
- Detect changes in employee eligibility or legal status
- Re-evaluate access privileges as job duties change
- Identify emerging behavioral red flags
Regular KYE reviews also foster employee confidence, everyone knows the standards of integrity and trust apply evenly. This culture of vigilance enables us to respond quickly to potential issues before they cause harm. Investing in continuous KYE isn’t just about compliance: it’s about future-proofing our business against fraud, insider threats, and reputational risk. Organizations that value ongoing verification build safer, more resilient teams.
Know Your Employee (KYE) Frequently Asked Questions
What is KYE and why is it important for businesses?
KYE (Know Your Employee) is the process of verifying employee identities, credentials, and backgrounds to ensure trust and compliance. It helps prevent internal fraud, insider threats, and safeguards sensitive operations from day one.
How does KYE differ from KYC and KYB?
While KYC verifies customers and KYB verifies business partners, KYE focuses internally on employees. It involves background checks and continuous monitoring to prevent insider risks and ensure workplace integrity.
What are the key elements of a robust KYE framework?
A strong KYE program includes identity verification, credential and background checks, ongoing monitoring, access control management, and staff training on KYE policies to reduce vulnerabilities and comply with regulations.
How do biometric and document verification enhance employee onboarding security?
Combining biometric data like facial recognition with document authentication helps detect forged credentials instantly, preventing fraudulent access and strengthening compliance during the onboarding process.
Can KYE help organizations comply with Anti-Money Laundering (AML) regulations?
Yes, KYE includes ongoing employee monitoring and documented screening processes that fulfill AML requirements by detecting suspicious activities and maintaining transparent audit trails for regulatory compliance.
What technologies are used to automate and streamline the KYE process?
Technologies such as AI-powered verification platforms, optical character recognition, digital onboarding portals, automated alert systems, and seamless HR integrations enhance efficiency and accuracy in employee verification.