-
How to Verify Age Without ID Securely
Many websites only need one answer: is this person old enough? They do not always need a passport scan, driver’s…
-
How to Verify Age Without ID Securely
-
What Is Deepfake Detection? How AI Identifies Synthetic and Manipulated Media
-
Biometric Authentication in Banking: How It Works and Why Banks Are Adopting It
-
What Is Liveness Detection? A Complete Guide to How It Works
-

What Is a Biometric ID? How It Works and Why It’s Replacing Traditional IDs
-
KYE (Know Your Employee): The Essential Guide to Employee Verification, Compliance, and Risk Mitigation
-
Passwordless Authentication: The Future of Secure Access and User Experience
-
Homomorphic Encryption: The Future of Secure Data & Private Computing
-
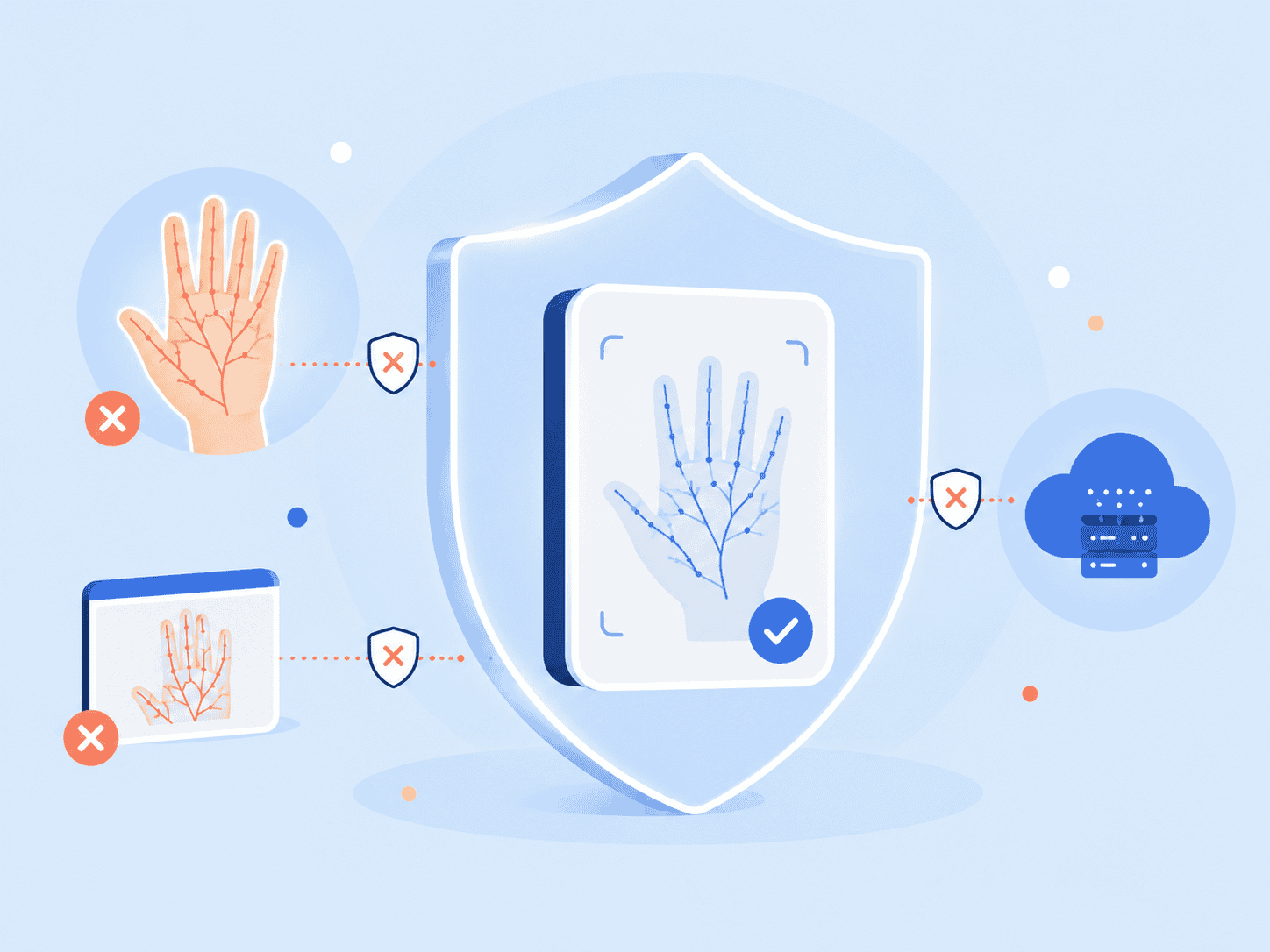
What Is Palm Biometrics? Palm Verification Explained
-
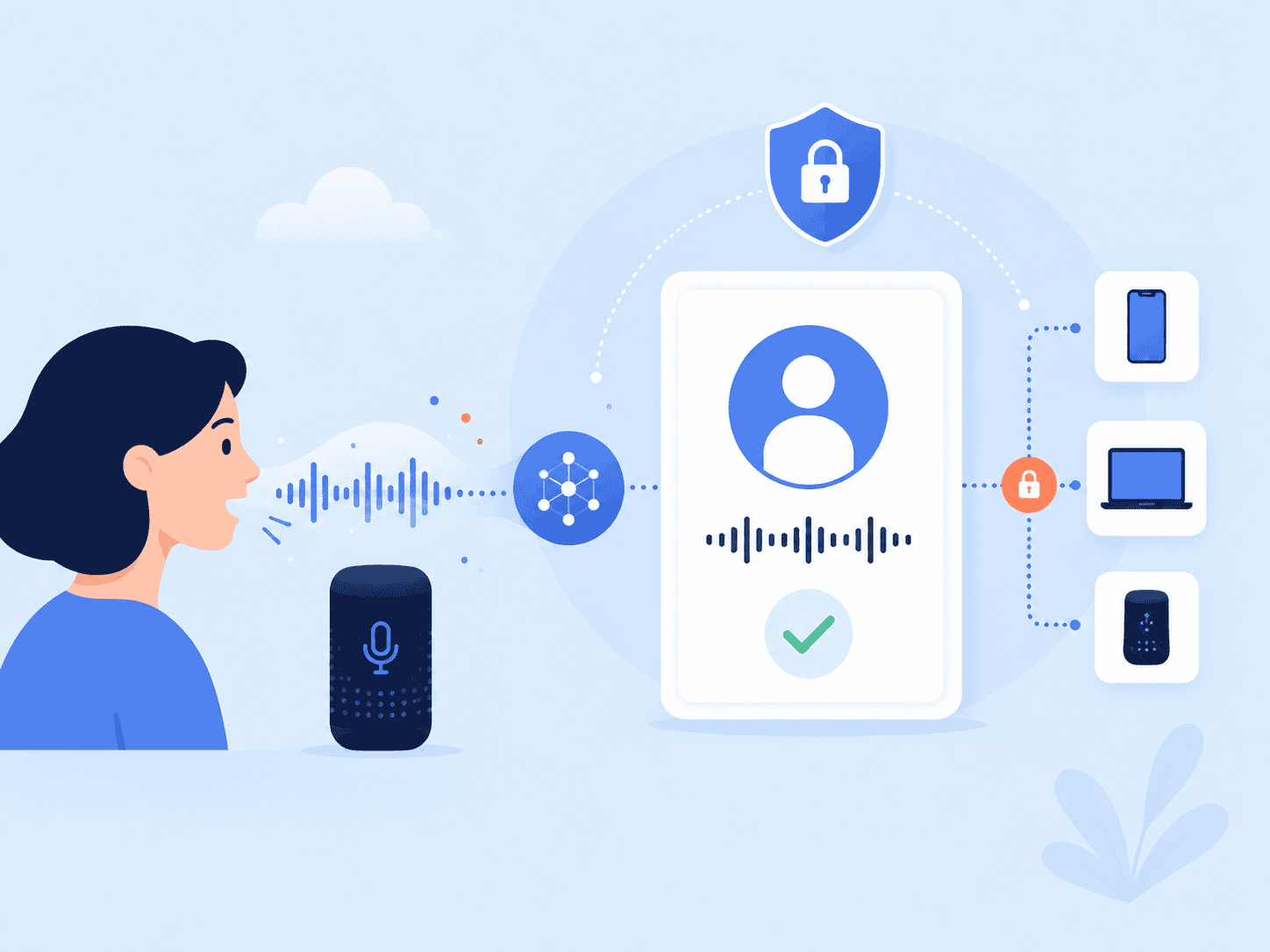
Voice Recognition Explained: How Speech Technology Works
-

Identity Assurance Explained: How Levels of Assurance Build Trust in the Digital Age
-

Anonymization Explained: How to Protect Sensitive Data and Ensure GDPR Compliance
-

Empowering Security: Identity Authentication and Why It’s Critical in 2026
-

Privacy-Preserving Strategies: Secure Data Sharing & AI Explained
-
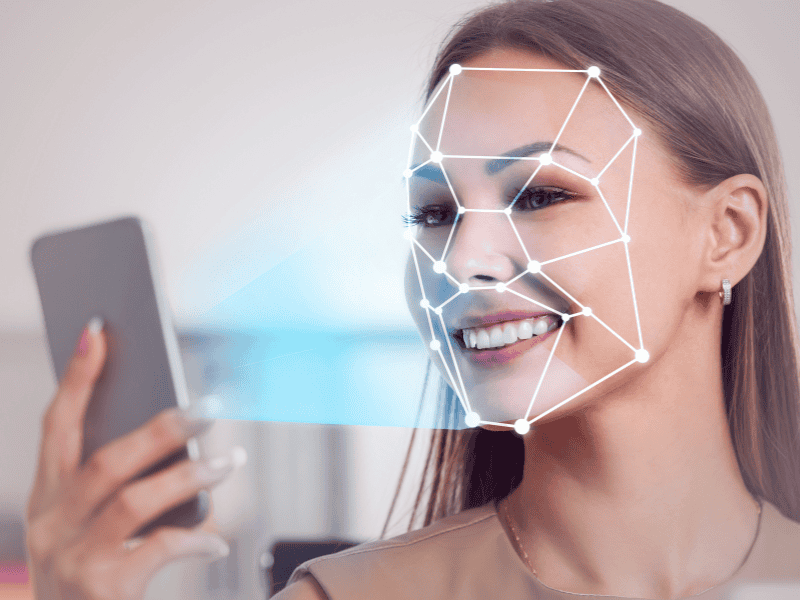
Facial Biometrics Explained: How Face Recognition Is Shaping Security